 MRT
MRT
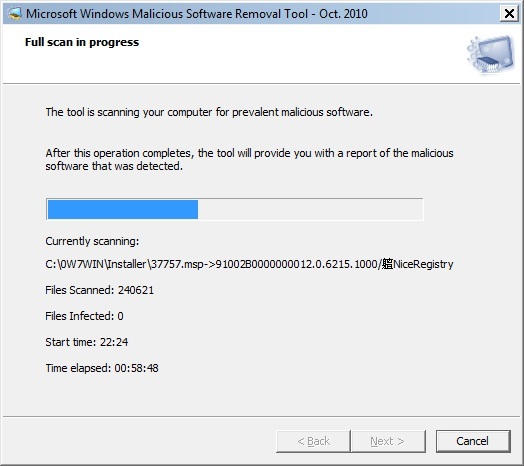
Just 3 letters you need to know – MRT
That is right, just type MRT.exe in you Start – Run box. Why they hide it so deep? Why there is no easy answer anywhere on the Internet?
The program is located in %WinDir%\System32\MRT.exe
Once again, to run Malicious Software Removal Tool type MRT in your Start – Run box.
In this article I am going to:
– Accumulate information about annoying files that push themselves in the registry;
– Show how to write a small CMD script that will continuously clean your registry Run locations;
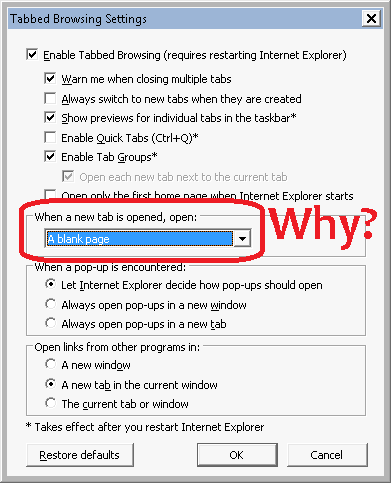
– Describe how to secure your Internet Explorer to lower possibility of malware infection;
– Demonstrate how to rename your CMD.EXE to prevent brutal attacks.
etMon.exe
I found this file link in registry at [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run], but no actual file in %WinDir%\etMon.exe exists.
After extensive search, I found a reference to this file inside:
%WinDir%\System32\DriverStore\FileRepository\etvideo.inf_amd64_neutral_e44d40c741c6982c modified on 9/21/2010.
and
C:\0W7WIN\inf\oem7.inf also modified 9/21/2010
It appears to be a device driver for “eMPIA Technology” (?) This is a company in Taiwan that doesn’t have an English web site (www.empiatech.com). Very suspicious. There is one reference to this company on Microsoft social blog – eMPIA Technology Inc.
Took this one out of the registry.
mctadmin.exe
I fount link to this file in Windows 7 registry at:
HKEY_USERS\S-1-5-20\Software\Microsoft\Windows\CurrentVersion\RunOnce
The is located in %WinDir%\System32\mctadmin.exe
There is no documentation on Microsoft site about this file. Date stamp and Properties appears to be in line with other files in this directory.
User S-1-5-20 is a legitimate NetworkService user. It might explain, why this RunOnce never get reset. This user never logins in interactively. Only as a service. I am leaving this one along.
I just found an explanation about this utility at http://technet.microsoft.com/en-us/library/dd799277(WS.10).aspx
This appears to be a legitimate Microsoft tool related to manipulation of Windows 7 installation packs (installation images).
ielowutil.exe
This EXE runs as a service in Windows 7 64-bit.
File is located in %ProgramFiles(x86)%\Internet Explorer\ielowutil.exe
File is dated 7/13/2009 as many other files in that directory.
There is not such file on Windows XP with IE8.
Microsoft gives a very technical answer about this file (sharing cookies across integrity levels), but it is confirmed on a legitimate Microsoft site:
Summary: no action is needed. Let it run as a service in Windows 7.

Be the first to comment